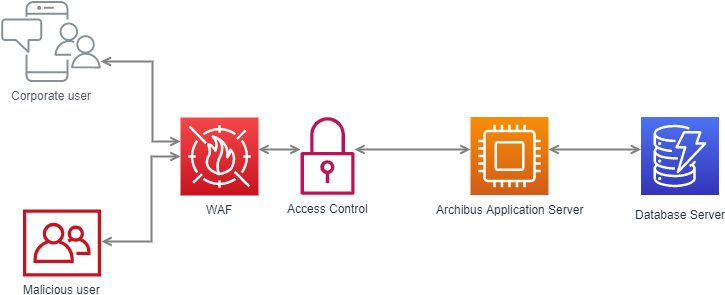
Web application firewall (WAF)
Web application firewall (WAF) inspects all traffic. WAF enables bot access control and defends the application against OWASP Top 10 threats like:
- SQL injection,
- cross-site scripting,
- illegal resource access,
- remote file inclusion.
Additionally, WAF helps companies become PCI DDS (Payment Card Industry Data Security Standard) compliant.
How does it work?
The WAF inspects http(s) traffic before it is allowed towards the application server. Reguests like GET and POST are sent through the firewall, where the traffic is analized against a ruleset to identify and filter out malicious web traffic. The ruleset includes patterns which match againt SQL injections, cross-site scripting, remote file inclusions, etc.
WAF uses dynamic application profiling in order to automatize the attack detection and minimize false positives. The Dynamic application profiling learns all the details of the application, for example the directories, URLs, parameters and user inputs. This allows to detect attacks with exceptional accuracy and block only bad traffic.
Benefits
A Web Application Firewall provides critical protection for any online application that must securely handle its private data inside. The extra security layer insures safeguarding a company’s reputation and position on the market. Attacks againt the application might result in fraud or data theft.
As You may know, Archibus application receives security updates very seldom so it it is essential to provide protection with other means, like WAF. For examle, SQL injections, which have been discovered in Archibus v24.1 are detected and blocked by the Web Application Firewall.
Archibus Solution Centre Hosting Services OU
Valukoja 8 – 8 and 13. floor, B-lift
11415 Tallinn – Estonia – EU
Content
Company